When Quantum Strikes: Why Bitcoin Must Revamp Before the Clock Runs Out
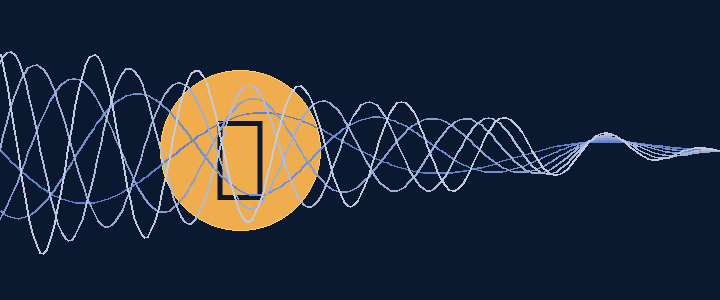
The rise of quantum computing isn’t science fiction anymore. As the technology matures, it threatens to undermine the cryptography that keeps Bitcoin secure. Today’s Bitcoin relies on algorithms like ECDSA for signatures and SHA-256 for hashing. These methods are robust against classical computers, but future quantum computers could run algorithms like Shor’s to derive private keys from public keys. That means a sufficiently advanced adversary could steal coins outright or fake signatures.
A hidden time bomb
Many early Bitcoin addresses still expose their public keys. If a quantum attacker harvests those public keys today and stores them until quantum hardware catches up, those wallets could be drained without warning. Even the simple act of sending a transaction reveals your public key until the transaction is confirmed. This vulnerability grows with time as more coins accumulate in exposed addresses.
“Not yet” isn’t good enough
Because quantum computers aren’t breaking Bitcoin today, some developers assume they have years to react. But Bitcoin’s global coordination and consensus process moves slowly. By the time the threat becomes obvious, it may be too late to roll out a coordinated upgrade. Attackers may also be collecting data now for a future “harvest now, decrypt later” attack.
What Bitcoin should do – ASAP
• Adopt post‑quantum cryptography: The community should test and implement quantum‑resistant signature schemes and hashing algorithms well before they’re needed. Lattice‑based and hash‑based signatures are promising candidates.
• Plan a migration window: There should be a defined period where vulnerable legacy addresses can be moved to safe ones before older formats are deprecated. This gives users a clear timeline to secure their funds.
• Raise awareness: Holders who reuse addresses or have exposed public keys need to move their funds now. Education and tooling to make that easy are critical.
• Build consensus early: Changing Bitcoin’s core cryptography requires miners, node operators, wallets, exchanges and custodians to align. Discussions and proposals must begin now to avoid chaos later.
The cost of doing nothing
If the network waits until quantum machines are breaking keys in the wild, the fallout will be immense. Large holders could see their coins stolen, and trust in Bitcoin’s security model could collapse. A rushed upgrade under duress increases the risk of forks and fragmentation. The stakes are too high to ignore.
Why CryptoAlleys is talking about this
CryptoAlleys isn’t just a listing site—we’re a community dedicated to the future of crypto. Highlighting existential risks like quantum computing is part of our mission to ensure that the ecosystem remains vibrant and secure. By discussing these issues openly, we can spur the collaboration needed to future‑proof Bitcoin and other blockchains.
Next steps
If you hold Bitcoin, avoid reusing addresses and stay informed about quantum‑resistant cryptography. Developers and researchers: join the conversation about implementing and testing post‑quantum signature schemes. CryptoAlleys will continue covering this topic as it evolves and plans to host a live discussion in early 2026.